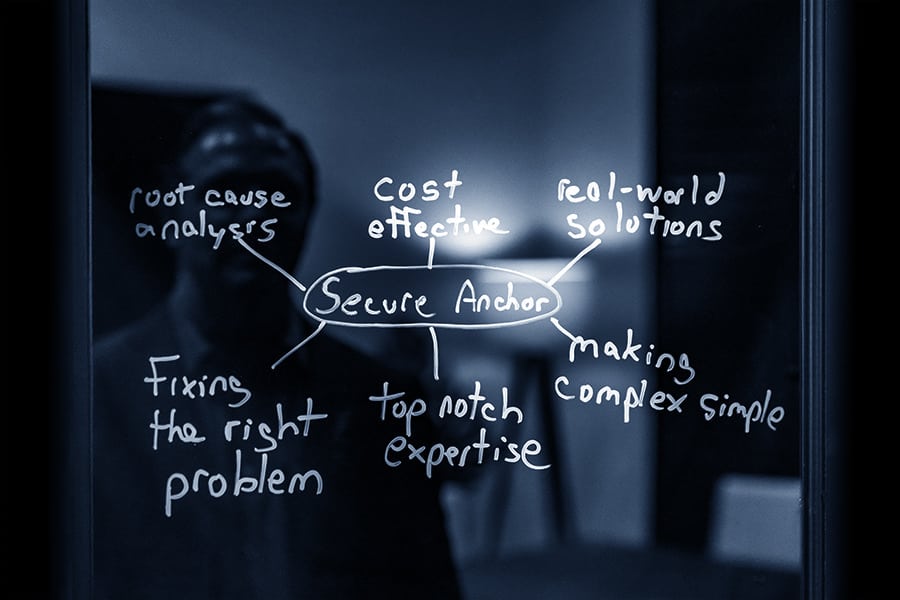
With over 15 years of cybersecurity expertise, there is no problem that we cannot solve with a creative cost-effective solution.
However, you have to wonder if they have the proven expertise to help you?
Secure Anchor is a premiere cybersecurity company founded by Dr. Cole with one focus, to make organizations, businesses and individuals safe in cyber space.
Many business leaders are unsure how to protect their business online; we give them the skills needed to improve their cybersecurity which will keep their business running smoothly.
We Have Worked With





With cybersecurity being an in demand area, new cybersecurity consulting companies appear on a regular basis. However, you have to wonder if they have the proven expertise to help you?
Secure Anchor is a premiere cybersecurity company founded by Dr. Cole with one focus, to make organizations, businesses and individuals safe in cyber space. We specialize in helping organizations understand the importance of cybersecurity and implement effective solutions.
Dr. Cole and Secure Anchor have the proven expertise to help solve your cybersecurity challenge. As a professional hacker for the CIA, he understands how attackers think and helps provide defensive solutions to keep you one step ahead of your enemy.
Secure Anchor has been trusted by some of the top businesses in the world. We can help you too!
how it works
Get in Touch
So we can schedule a call to learn more about you.

We discuss your goals and needs
We will learn more about your business needs, ideas, and goals.
Improve Your Security
Your company will receive the cybersecurity expertise it needs to be secure.
Expert Witness

Consulting
Keynote


Training